The Access Point
We eat, sleep, and breathe technology. We also write about it.
Read our blog to stay up-to-date on the latest and greatest in IT, Atomic Data, and our charitable work.
Read our blog to stay up-to-date on the latest and greatest in IT, Atomic Data, and our charitable work.
Security Bulletins
Atomic Data is at the forefront of security monitoring and is here to inform you. Read this post to review the latest security bulletins.
The Importance of SOC® Attestation for Managed Service Providers and Their Clients in 2024
April 02, 2024
Industry
Products & Services
With more and more companies looking to move diverse facets of their IT operations to Managed Service Providers in 2024, one topic that often comes up is how your organization evaluates the security of a service provider's operations.
MARCH 28 – Understanding the 2024 VMware Broadcom Licensing Requirements & Partner Changes
Atomic Data has been invited as a Premier Partner into the Broadcom Advantage Partner Program for VMware Cloud Service Providers, allowing us to provide a white label resale solution to other VMware hosting providers not invited into the program.
Atomic Data Grows Game Day Roster, Signs Three New Soccer Clubs
February 29, 2024
News
The IT solutions provider recently secured partnership deals with Seattle Sounders FC, Sporting Kansas City, and Houston Dynamo FC.
INTER&Co Stadium to Enhance In-Venue Shopping Experience, Wi-Fi Infrastructure
February 21, 2024
News
Orlando City SC and the Orlando Pride have announced an enhancement to the fan experience at INTER&Co Stadium, becoming the first soccer-specific venue to offer Amazon’s Just Walk Out technology for retail.
Atomic Data Becomes Official IT Partner of Houston Dynamo, Houston Dash, and Shell Energy Stadium
February 20, 2024
News
The multi-year agreement provides the clubs with advanced IT services and support to further their operations.
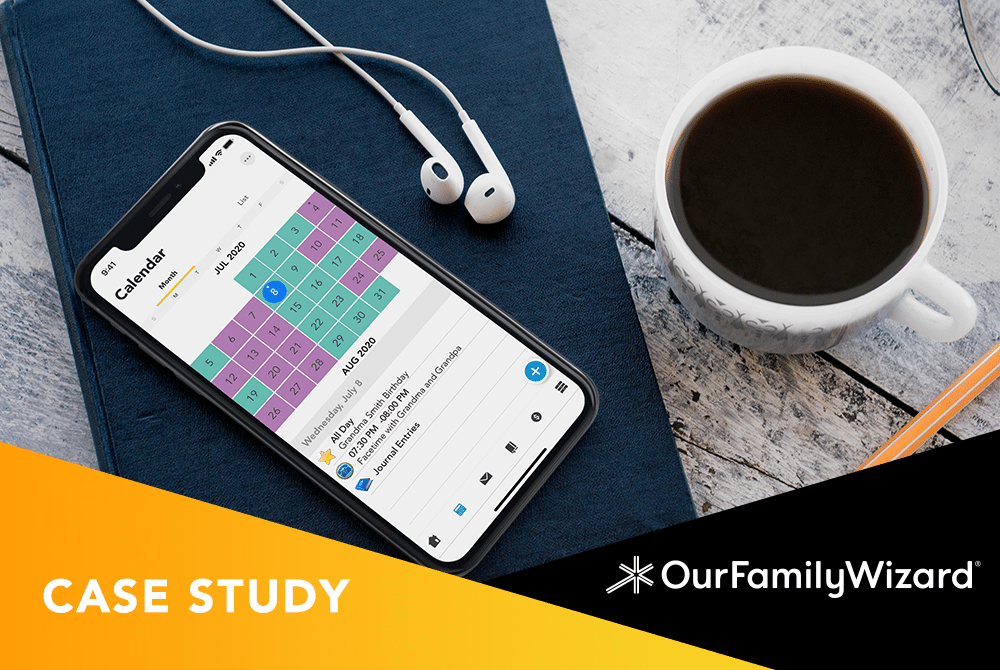
Moving seamlessly to Exchange Online
October 27, 2023
Case Studies
Read how Minneapolis company Our Family Wizard improved business efficiency by migrating to Exchange Online.
Connecting the Dots: How Morgan Kennedy Creates Community
October 20, 2023
Workforce Development
Morgan Kennedy, Chief Marketing and Growth Officer at Atomic Data and a Founder of the Twin Cities Chapter of Impact100, is bringing women together to create genuine and lasting connections through community.
Atomic Data Named Proud IT Provider of Orlando City SC and Orlando Pride
October 05, 2023
News
The multi-year agreement is an evolution of the existing partnership, with Atomic Data serving as the Club’s Virtual CIO and Owner’s Technology Rep since 2022.